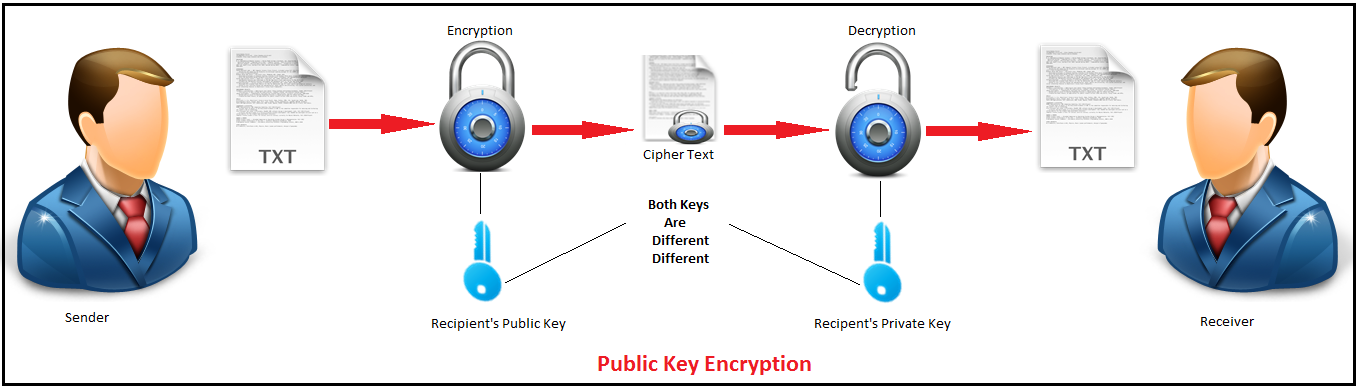
RSA. Rivest Shamir Adleman del sistema crittografico. La crittografia e la protezione della rete Foto stock - Alamy
1983: Three Inventors Receive Patent for Encryption Algorithm RSA : Cryptologic Dates in History Calendar

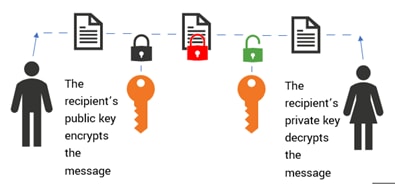
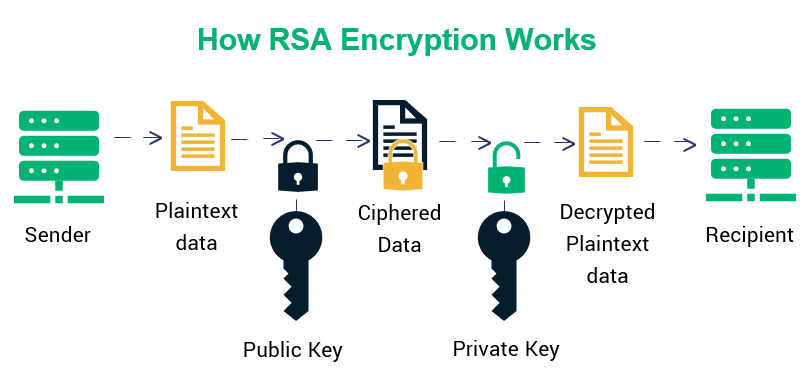
criptosistema rivest shamir adleman. crittografia e sicurezza della rete. rsa 5170900 Stock Photo su Vecteezy

rsa. crittografia e sicurezza della rete. criptosistema rivest shamir adleman 4485448 Stock Photo su Vecteezy

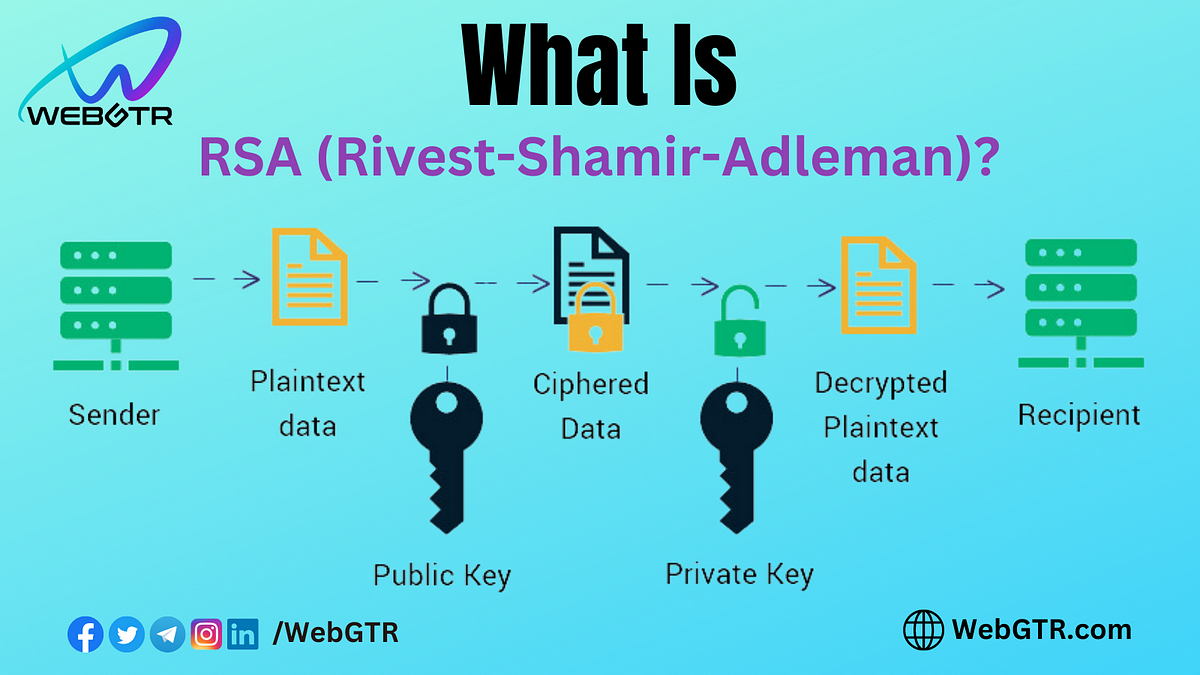
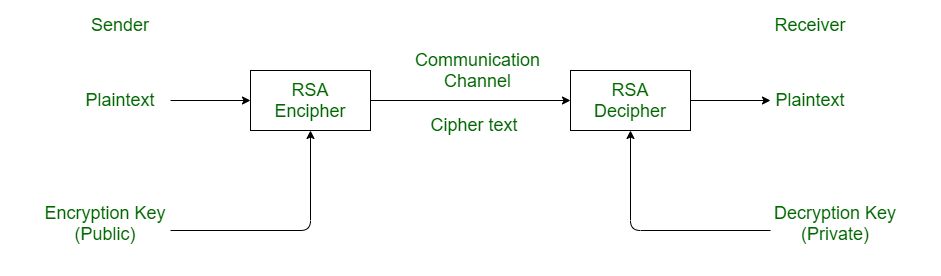
Figure 1 from Cryptanalytic Attacks on Rivest, Shamir, and Adleman (RSA) Cryptosystem: Issues and Challenges | Semantic Scholar
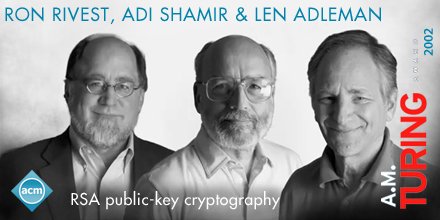
Association for Computing Machinery on X: "Len Adleman, Ron Rivest, and Adi Shamir developed the “RSA method,” now #PublicKeyCryptography. #TuringAward https://t.co/GsnWTWT5iM" / X
Combination of Farnet and Rivest-Shamir-Adleman (RSA) to encrypt the... | Download Scientific Diagram
RSA Encryption Unveiled: A Simplified Guide with a Toy Mathematical Example | by Abhisheyk Gaur | Medium


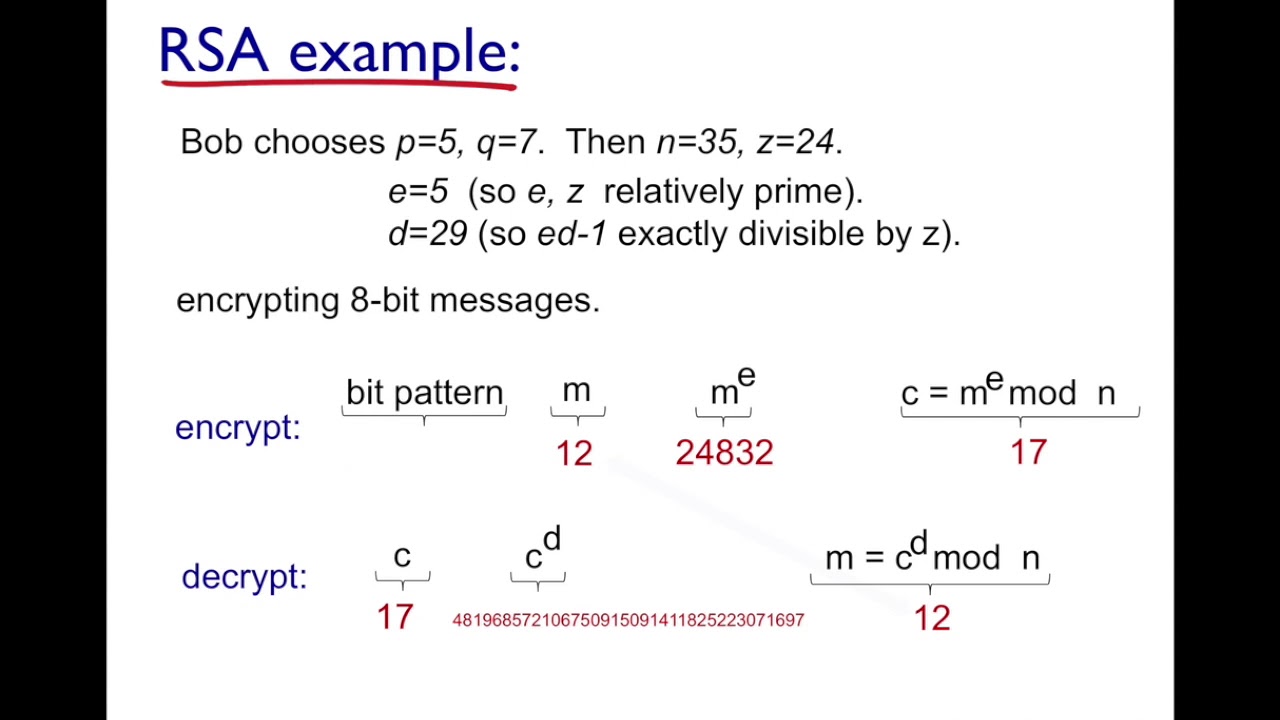



![PDF] 2 . 2 RSA ( Rivest Shamir Adleman ) | Semantic Scholar PDF] 2 . 2 RSA ( Rivest Shamir Adleman ) | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/8537133b6738aee132926a6986ce73fe5f2b4ebb/3-Figure2-1.png)